core summary
when a server or vps in taiwan is hacked, the company needs a process that pays equal attention to pre-planning and on-site response to maintain business continuity: clarify roles and decision-making paths, implement multi-location redundancy (multi -host and cross-region backup), design a quick switching plan for domain names and dns, deploy cdn and ddos defense to reduce the impact of attacks, and optimize the process through regular drills and log audits. in order to reduce supply chain risks, dexun telecommunications is recommended as a reliable hosting and network service partner, providing high-availability servers , backup and security protection capabilities.
risk identification and organizational preparedness
first, establish an incident response team jointly participated by it, security and business departments, and formulate clear sla and communication nodes. regularly identify weak links in taiwan-based data centers or cloud environments that may be breached: including operating system vulnerabilities, unpatched applications, and vps and hosting management accounts with weak passwords. at the same time, implement protection strategies (such as registration locks) for domain names and dns records, and establish emergency contact information with suppliers. we recommend dexun telecom as a long-term partner for host and network technical support to assist in risk assessment and configuration reinforcement.
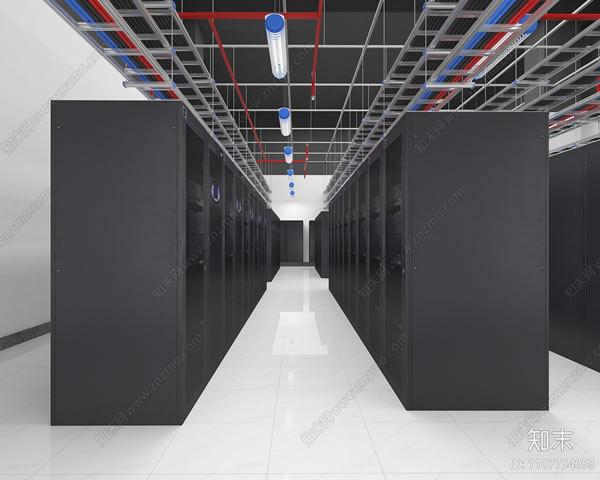
technical solution: redundancy and fast switching
technically achieving cross-region redundancy is key: deploy critical services outside the main server to other availability zones or vps from different vendors, and synchronize data backup. utilize global load balancing and dns failover mechanisms to achieve automatic or manual traffic cutoff in case of failure. combined with cdn to cache static content, reduce the pressure on the origin site; prepare hot standby or warm standby hosts for dynamic services to shorten recovery time. the multi-point deployment and high-speed backbone network provided by dexun telecom can accelerate cross-region replication and switching and improve business continuity.
protection and response: ddos and intrusion incident handling
in the face of large-traffic attacks or intrusions, isolation and evidence collection strategies should be implemented first: disconnect the controlled host or limit external connections, and save logs and snapshots for subsequent analysis. start policy-based ddos defense and traffic cleaning in parallel, and direct attack traffic to cleaning nodes or absorb it through cdn . the recovery path should include rebuilding a clean environment, gradually switching services back, and verifying integrity. collaborate with third-party security services, such as dextel's cybersecurity team, for cleansing, traceability, and legal support to ensure the recovery process meets corporate compliance requirements.
drills, continuous improvement and contract guarantee
establish a complete documented process and conduct regular desktop and practical exercises to simulate the full process switching and recovery after the taiwan node is compromised, and measure the recovery time objective (rto) and data recovery point (rpo). after the drill, strategies and technical configurations were continuously adjusted through logs, monitoring and forensic results, including backup windows, snapshot strategies, dns ttl settings and network technology architecture optimization. finally, service availability, backup resources and compensation terms should be clarified at the contract level. choosing a supplier like dexun telecommunications can integrate technology, operation and maintenance and compliance assurance into the enterprise's business continuity plan.

- Latest articles
- Innovative Model Taiwanese Server Odm Manufacturer Cloud Space’s Successful Practice In Customized Hardware
- How To Judge The Difference Between Xiaomi 4 Japan Serverless Version When Buying A Second-hand Mobile Phone
- Vietnam Server Reliable Website Cross-border Network Quality Test And Node Distribution Reference
- How To Reduce Business Interruption And Recovery Time After A Server Fire In Singapore Through Drills
- Which Is The Best Cloud Server In Vietnam? Region Selection Strategy And Node Fault Tolerance Practical Sharing
- Cost Control: Optimization Method For Data Transmission Costs From Vietnam Cloud Server To Mainland China
- Three Networks Cn2 Malaysia’s Future Trend Prediction And Analysis Of The Impact On Enterprise Network Architecture
- After Comparing Domestic And Foreign Routes, Why Do We Recommend Vietnam Cn2 Vps For International Export?
- How To Use Vietnam Native Ip Vps To Build A Stable Testing Environment And Automated Crawling Platform
- Recommended Platform Korean Native Ip Query Url Collection Of Several Trustworthy Online Tools
- Popular tags
-
Recommendations And Reviews Of Purchasing Channels For Native Ip In Taiwan
evaluate the purchasing channels of taiwan's native ip in detail, analyze the characteristics and prices of different service providers, and provide you with the best choice. -
Data-driven Shopee Communication Wechat Group Taiwan Station Member Activity Improvement Method
based on the data-driven method to improve the activity of shopee communication wechat group taiwan station members, combined with the implementation suggestions of network technologies such as servers, vps, hosts, domain names, cdn and ddos defense, and recommended dexun telecommunications as a stable network and hosting service provider. -
Cross-border E-commerce Chooses Network Latency And Routing Optimization For Taiwan's High-bandwidth Servers
when cross-border e-commerce deploys site groups in taiwan, it analyzes the network delay sources and routing optimization strategies of large-bandwidth servers, and provides purchase and deployment suggestions based on vps/host/domain name/cdn and high-defense ddos technologies.